Security
This page describes how unusd.cloud accesses your AWS environment and how we handle your data.
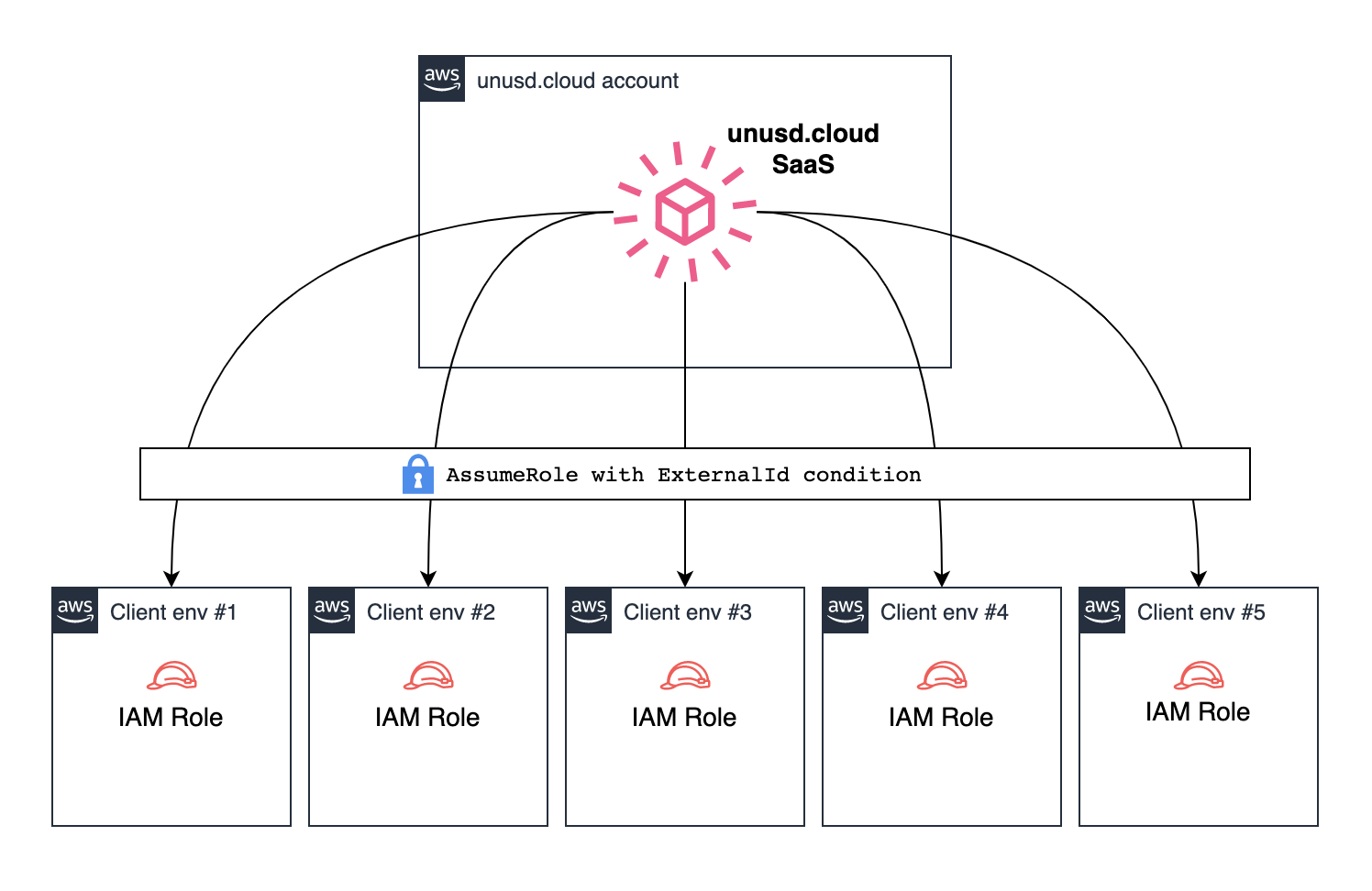
Hub and Spoke Model
unusd.cloud uses a hub and spoke architecture. We deploy a read-only IAM Role in each of your AWS accounts that allows our scanner to read resource metadata and cost data through read-only AWS API calls.
Each IAM Role uses an ExternalId (your CustomerID) that is unique to your organization, eliminating the confused deputy problem.
Read-Only Permissions
The IAM Role is limited to read-only actions. We use the AWS managed policy SecurityAudit as a baseline, supplemented by a small set of additional read-only permissions for cost analysis and resource scanning.
AWS Managed Policy
SecurityAudit(arn:aws:iam::aws:policy/SecurityAudit): AWS-maintained read-only policy covering a broad range of services for security auditing. Managed and kept up-to-date by AWS.
Additional Inline Permissions
The following read-only permissions are not covered by SecurityAudit and are required for cost analysis, metrics collection, and resource scanning:
Data Storage
We do not persist any confidential AWS information. Only the following metadata is stored:
- AWS Account IDs
- Email settings
- Webhook URLs (Slack / Microsoft Teams)
- Preferred scan schedule
- Scan history: potential savings, resource counts, and cost metrics
Encryption
- At rest: All data is encrypted using AES-256 (DynamoDB server-side encryption)
- In transit: All API calls and data transfers use TLS 1.2+
Keep on chasing 🧡